In today's fast-paced digital world, the ability to SSH device from anywhere has become an essential skill for IT professionals, remote workers, and tech enthusiasts alike. Secure Shell (SSH) is a cryptographic protocol designed to secure communication between devices over an unsecured network. It offers a powerful way to remotely manage servers, access files, and execute commands from virtually any location.
Whether you're troubleshooting a server issue from the comfort of your home or accessing critical files while traveling, SSH provides a reliable solution. Its robust encryption ensures that your data remains secure, even when transmitted across public networks.
This comprehensive guide will walk you through everything you need to know about SSH device from anywhere. From setting up your environment to troubleshooting common issues, we'll cover it all. By the end of this article, you'll have the knowledge and tools to confidently manage your devices remotely.
Table of Contents
- Introduction to SSH
- How SSH Works
- Setting Up SSH for Remote Access
- Securing Your SSH Connection
- Tools for SSH Device from Anywhere
- Advanced SSH Techniques
- Troubleshooting SSH Issues
- Best Practices for SSH
- Alternatives to SSH
- Conclusion
Introduction to SSH
Secure Shell (SSH) is a network protocol that allows users to access and manage remote devices securely. Originally developed in 1995 as a replacement for less secure protocols like Telnet, SSH has since become the standard for remote access. It provides a secure channel over which users can execute commands, transfer files, and manage network devices.
SSH operates on port 22 by default and uses encryption algorithms to ensure the confidentiality and integrity of data transmitted between devices. Its widespread adoption is due to its reliability, security, and versatility. Whether you're a system administrator or a developer, SSH is an indispensable tool for remote management.
One of the key advantages of SSH is its ability to work across different operating systems. Whether you're using Linux, macOS, or Windows, SSH can be configured to meet your specific needs. This cross-platform compatibility makes it an ideal choice for organizations with diverse IT environments.
How SSH Works
Understanding how SSH works is crucial for effectively using it to access your device from anywhere. At its core, SSH establishes a secure connection between a client and a server using public-key cryptography. Here's a step-by-step breakdown of the process:
- Connection Initiation: The client initiates a connection to the server by specifying the IP address or domain name.
- Key Exchange: The client and server exchange cryptographic keys to establish a secure session.
- Authentication: The user is authenticated using either a password or a public/private key pair.
- Encrypted Communication: Once authenticated, all communication between the client and server is encrypted to prevent eavesdropping.
This process ensures that even if the connection is intercepted, the data remains secure. SSH also supports various encryption algorithms, allowing users to choose the level of security that best suits their needs.
Encryption Methods in SSH
SSH supports multiple encryption methods, each with its own strengths and weaknesses. Some of the most commonly used algorithms include:
- AES (Advanced Encryption Standard)
- ChaCha20
- Blowfish
Selecting the appropriate encryption method depends on factors such as performance requirements and security concerns. For most use cases, AES is recommended due to its balance of speed and security.
Setting Up SSH for Remote Access
Setting up SSH for remote access involves several key steps. First, you'll need to ensure that SSH is installed and configured on both the client and server devices. Here's a detailed guide to help you get started:
On Linux and macOS:
- SSH is typically pre-installed on these operating systems. To verify, open a terminal and type `ssh`.
- Enable SSH on your server by editing the `/etc/ssh/sshd_config` file and restarting the SSH service.
On Windows:
- Starting with Windows 10, SSH can be installed via the Windows Features menu.
- Alternatively, you can use third-party clients like PuTTY for SSH connectivity.
Once SSH is installed, you'll need to configure firewall settings to allow incoming connections on port 22. Additionally, consider changing the default port for added security.
Securing Your SSH Connection
While SSH is inherently secure, there are additional steps you can take to further protect your connections. Here are some best practices for securing SSH:
- Disable Password Authentication: Use public-key authentication instead of passwords to prevent brute-force attacks.
- Change Default Port: Moving SSH from port 22 to a non-standard port reduces the risk of automated attacks.
- Use a Firewall: Configure your firewall to restrict SSH access to trusted IP addresses.
- Implement Two-Factor Authentication: Add an extra layer of security by requiring a second form of verification.
By following these practices, you can significantly reduce the risk of unauthorized access to your devices.
SSH Security Best Practices
In addition to the measures mentioned above, consider implementing the following practices:
- Regularly update your SSH software to patch known vulnerabilities.
- Monitor SSH logs for suspicious activity.
- Limit the number of login attempts to prevent brute-force attacks.
These practices, combined with proper configuration, ensure that your SSH connections remain secure.
Tools for SSH Device from Anywhere
There are several tools available that make it easier to SSH device from anywhere. These tools offer additional features such as session management, file transfer, and terminal emulation. Some of the most popular options include:
- PuTTY: A free and open-source SSH client for Windows.
- SSHFS: Allows you to mount remote file systems over SSH.
- TunnelBear: A secure tunneling tool that simplifies SSH connections.
Each of these tools has its own strengths, so the best choice depends on your specific needs. For example, if you need to transfer files, SSHFS might be the most suitable option.
Comparing SSH Tools
When selecting an SSH tool, consider factors such as ease of use, feature set, and compatibility with your operating system. Below is a comparison of some popular SSH clients:
- PuTTY: Ideal for Windows users due to its simplicity and robust feature set.
- Termius: A cross-platform SSH client that supports iOS, Android, macOS, and Windows.
- Bitvise: Offers advanced features like SFTP and terminal emulation.
By evaluating these options, you can choose the tool that best fits your workflow.
Advanced SSH Techniques
For experienced users, SSH offers a range of advanced techniques to enhance productivity and security. Some of these techniques include:
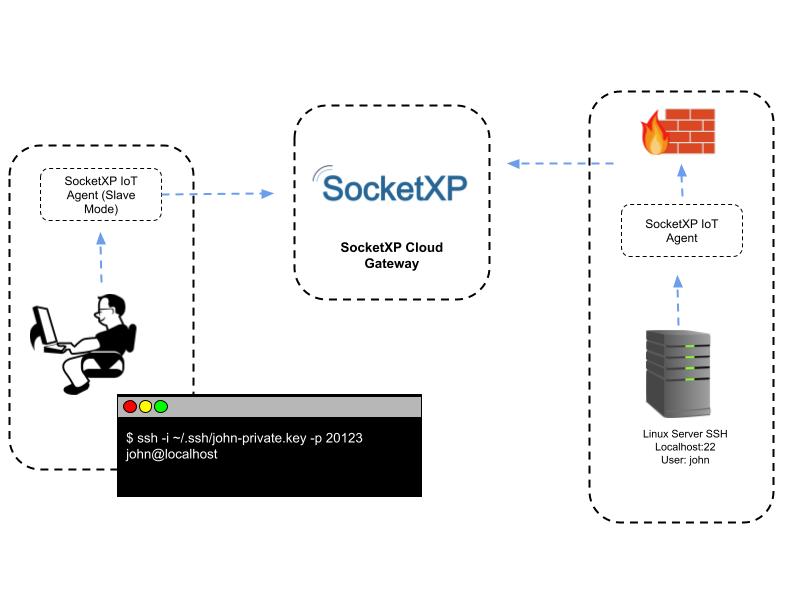
- SSH Tunneling: Create secure tunnels to access services behind firewalls.
- SSH Keys Management: Manage multiple SSH keys for different devices.
- SSH Config File: Simplify connection management by defining aliases and configurations.
These techniques allow you to streamline your workflow and improve the efficiency of your remote access operations.
SSH Tunneling Explained
SSH tunneling, also known as port forwarding, allows you to securely access services on a remote network. There are three types of SSH tunneling:
- Local Forwarding: Forwards a local port to a remote server.
- Remote Forwarding: Forwards a remote port to a local machine.
- Dynamical Forwarding: Creates a SOCKS proxy for secure browsing.
Understanding these techniques can help you overcome network restrictions and securely access remote resources.
Troubleshooting SSH Issues
Even with proper configuration, SSH issues can arise. Common problems include connection timeouts, authentication failures, and permission errors. Here's how to troubleshoot these issues:
- Check Firewall Settings: Ensure that the necessary ports are open and accessible.
- Verify SSH Configuration: Review the `/etc/ssh/sshd_config` file for errors.
- Test Connectivity: Use tools like `ping` and `traceroute` to diagnose network issues.
By systematically addressing these issues, you can quickly restore SSH functionality.
Common SSH Errors
Some of the most frequently encountered SSH errors include:
- Permission Denied: Typically caused by incorrect file permissions or mismatched keys.
- Connection Refused: Indicates that the SSH service is not running or the port is blocked.
- Host Key Verification Failed: Occurs when the server's host key does not match the stored key.
Understanding the root cause of these errors is key to resolving them effectively.
Best Practices for SSH
To ensure optimal performance and security, follow these best practices for SSH:
- Regularly audit SSH configurations and permissions.
- Use strong, unique passwords or key pairs for authentication.
- Limit SSH access to trusted users and devices.
By adhering to these practices, you can minimize risks and maximize the benefits of SSH.
Alternatives to SSH
While SSH is the gold standard for remote access, there are alternative solutions worth considering:
- RDP (Remote Desktop Protocol): Ideal for graphical remote access on Windows systems.
- VNC (Virtual Network Computing): Provides remote access to graphical interfaces across platforms.
- Web-Based Solutions: Tools like TeamViewer and AnyDesk offer cross-platform remote access with a user-friendly interface.
Each of these alternatives has its own advantages and limitations, so the best choice depends on your specific requirements.
Conclusion
In conclusion, the ability to SSH device from anywhere is a powerful skill that can greatly enhance your productivity and flexibility. By understanding how SSH works, configuring it securely, and utilizing advanced techniques, you can effectively manage your devices remotely. Remember to follow best practices and stay informed about the latest developments in SSH security.
We encourage you to share your experiences and insights in the comments below. Additionally, feel free to explore other articles on our site for more tips and tutorials. Together, let's continue to expand our knowledge and improve our remote access capabilities.