Controlling IoT devices behind a firewall is becoming increasingly important as smart technology continues to evolve. With the growing number of connected devices, ensuring secure communication while maintaining accessibility is critical. Whether you're managing a smart home or an industrial IoT network, understanding how to configure your firewall properly can significantly enhance your security posture.
In this digital age, the Internet of Things (IoT) has revolutionized the way we interact with technology. From smart thermostats to industrial sensors, IoT devices have become integral to both personal and business environments. However, this integration also introduces new security challenges that must be addressed.
This article aims to provide a comprehensive guide on how to control IoT devices behind a firewall. We'll explore key concepts, best practices, and practical steps to secure your IoT infrastructure while maintaining seamless connectivity. By the end of this article, you'll have the knowledge and tools necessary to protect your network and devices effectively.
Table of Contents
- What is IoT?
- Understanding Firewalls
- Securing IoT Devices Behind a Firewall
- How to Configure Your Firewall for IoT
- The Importance of Network Segmentation
- Best Practices for IoT Security
- Common Issues and Solutions
- Tools and Software for IoT Management
- Future Trends in IoT Security
- Conclusion
What is IoT?
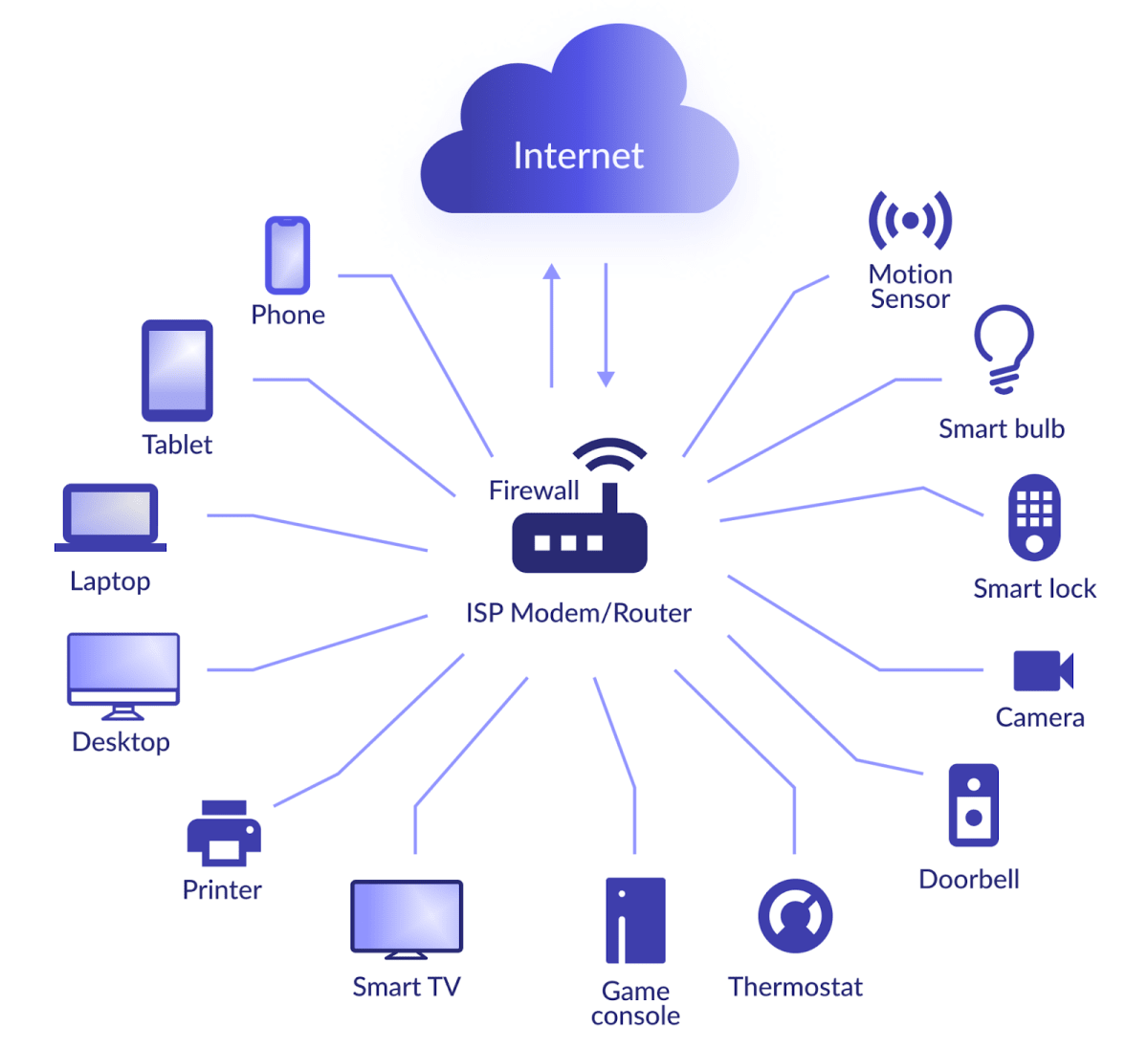
The Internet of Things (IoT) refers to the network of physical devices, vehicles, home appliances, and other items embedded with sensors, software, and connectivity that enables them to exchange data. These devices range from simple household gadgets like smart light bulbs to complex industrial equipment. IoT devices enhance convenience and efficiency but also introduce unique security challenges.
Key Characteristics of IoT Devices
- Interconnectivity: IoT devices communicate with each other and with central systems.
- Automation: Many IoT devices operate autonomously, performing tasks without human intervention.
- Data Collection: IoT devices gather vast amounts of data, which can be used for analytics and decision-making.
As IoT adoption grows, so does the need for robust security measures, particularly when it comes to controlling these devices behind a firewall.
Understanding Firewalls
A firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. It acts as a barrier between a trusted network and untrusted external networks, such as the internet. Firewalls play a crucial role in protecting IoT devices by filtering traffic and preventing unauthorized access.
Types of Firewalls
- Packet Filtering Firewalls: Examine packets at the network layer and either allow or deny them based on predefined rules.
- Stateful Inspection Firewalls: Track active connections and evaluate packets in the context of these connections.
- Application-Level Gateways: Operate at the application layer, providing deeper inspection and control over specific applications.
Understanding the different types of firewalls and their capabilities is essential for effectively securing IoT devices.
Securing IoT Devices Behind a Firewall
Securing IoT devices behind a firewall involves a combination of proper configuration, network segmentation, and regular maintenance. By implementing these strategies, you can significantly reduce the risk of unauthorized access and data breaches.
Steps to Secure IoT Devices
- Identify all IoT devices on your network and document their configurations.
- Implement strong authentication mechanisms to ensure only authorized users can access the devices.
- Regularly update firmware and software to patch known vulnerabilities.
According to a report by Gartner, the number of IoT devices is expected to exceed 25 billion by 2025, making security a top priority for organizations and individuals alike.
How to Configure Your Firewall for IoT
Configuring your firewall for IoT involves setting up rules that allow necessary traffic while blocking potential threats. This process requires a thorough understanding of your network architecture and the specific needs of your IoT devices.
Best Practices for Firewall Configuration
- Use specific IP addresses and ports to limit access to IoT devices.
- Enable logging to monitor traffic and detect suspicious activity.
- Regularly review and update firewall rules to adapt to changing security requirements.
For example, if you have a smart thermostat, you might configure your firewall to allow only HTTPS traffic on port 443 to ensure secure communication.
The Importance of Network Segmentation
Network segmentation involves dividing a network into smaller subnetworks to improve security and performance. By isolating IoT devices from other parts of the network, you can limit the potential impact of a security breach.
Benefits of Network Segmentation
- Reduces the attack surface by limiting access to sensitive data and systems.
- Improves network performance by reducing congestion and latency.
- Facilitates easier monitoring and management of IoT devices.
Research from IBM indicates that organizations that implement network segmentation experience fewer and less severe security incidents compared to those that do not.
Best Practices for IoT Security
In addition to firewall configuration and network segmentation, there are several best practices you can adopt to enhance IoT security:
Key Recommendations
- Change default passwords and use strong, unique credentials for each device.
- Enable encryption for all data transmissions to protect sensitive information.
- Regularly back up device configurations and data to prevent data loss in case of a breach.
These practices, combined with a proactive security strategy, can help safeguard your IoT infrastructure against potential threats.
Common Issues and Solutions
Managing IoT devices behind a firewall can present several challenges, including connectivity issues, configuration errors, and compatibility problems. Understanding these common issues and their solutions is essential for maintaining a secure and functional IoT network.
Addressing Connectivity Problems
- Check firewall rules to ensure they allow necessary traffic for IoT devices.
- Verify that devices are correctly configured and connected to the network.
- Consult device documentation for troubleshooting tips and support resources.
For instance, if an IoT device fails to connect to the internet, reviewing firewall logs can help identify and resolve the issue.
Tools and Software for IoT Management
Several tools and software solutions are available to assist with managing and securing IoT devices behind a firewall. These tools provide features such as device monitoring, threat detection, and automated updates.
Popular IoT Management Platforms
- IBM Watson IoT Platform: Offers advanced analytics and integration capabilities.
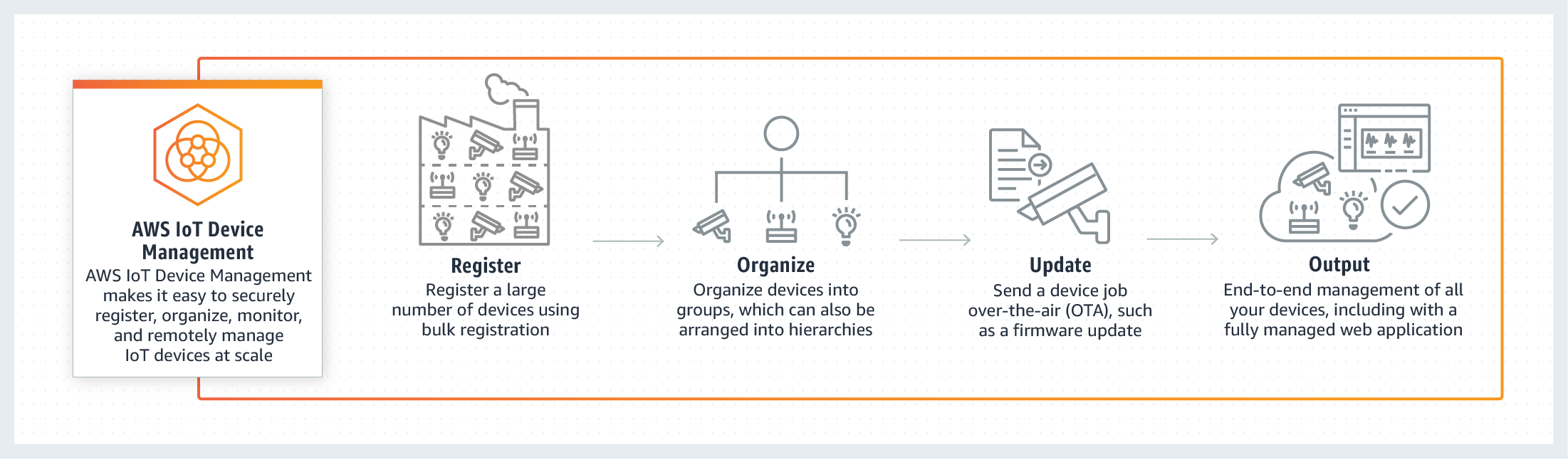
- Amazon Web Services (AWS) IoT: Provides scalable and secure connectivity for IoT devices.
- Microsoft Azure IoT Hub: Enables device management and data processing in the cloud.
Using these platforms can simplify the management of large IoT networks and enhance overall security.
Future Trends in IoT Security
The landscape of IoT security is continually evolving, with new technologies and strategies emerging to address emerging threats. Some of the key trends to watch include:
Innovations in IoT Security
- Artificial Intelligence (AI) and Machine Learning (ML) for threat detection and response.
- Blockchain technology for secure data storage and transaction verification.
- Zero Trust Architecture to minimize reliance on traditional perimeter security.
Staying informed about these trends can help you prepare for the future of IoT security and ensure your network remains protected.
Conclusion
Controlling IoT devices behind a firewall requires a comprehensive approach that encompasses proper configuration, network segmentation, and adherence to best practices. By implementing the strategies outlined in this article, you can enhance the security of your IoT infrastructure and protect against potential threats.
We encourage you to take action by reviewing your current firewall settings and implementing the recommended security measures. Share your thoughts and experiences in the comments below, and consider exploring other articles on our site for additional insights into IoT security.
Remember, securing your IoT devices is not a one-time task but an ongoing process. Stay vigilant and proactive to ensure the safety and functionality of your connected world.