In today's interconnected world, the ability to access IoT devices securely through SSH on AWS is critical for maintaining robust cybersecurity practices. As more organizations adopt cloud-based solutions, ensuring secure access to IoT devices has become a top priority. This guide explores how to establish secure access for IoT devices using SSH on AWS, providing practical insights and best practices.
As technology continues to evolve, the Internet of Things (IoT) has revolutionized the way we interact with devices. However, with the increasing number of connected devices comes the challenge of securing them. Accessing IoT devices through SSH on AWS offers a secure solution for managing and maintaining these devices remotely.
This article delves into the intricacies of Access IoT SSH AWS, offering step-by-step guidance and expert insights to help you implement secure connectivity solutions. Whether you're a developer, IT professional, or cybersecurity enthusiast, this guide will equip you with the knowledge needed to protect your IoT infrastructure.
Table of Contents
- Introduction to IoT SSH AWS
- Why Secure Access Matters
- Setting Up SSH on AWS
- Configuring IoT Devices for SSH
- Best Practices for Secure IoT SSH AWS
- Common SSH AWS Issues and Solutions
- Enhancing Security with SSH Keys
- Integrating IoT with AWS Services
- Monitoring and Managing IoT SSH Connections
- Future of IoT SSH AWS
Introduction to IoT SSH AWS
The integration of IoT devices with cloud platforms like AWS has transformed the landscape of modern technology. Secure Shell (SSH) plays a pivotal role in ensuring that these devices can be accessed and managed remotely without compromising security. Access IoT SSH AWS combines the flexibility of IoT with the robust security features of AWS, creating a powerful solution for businesses and individuals alike.
SSH is a cryptographic network protocol that facilitates secure communication between devices over an unsecured network. When applied to IoT devices hosted on AWS, SSH provides a secure channel for data transfer and device management. This section explores the fundamentals of IoT SSH AWS, including its benefits and applications.
Key Benefits:
- Enhanced security through encrypted communication.
- Remote access capabilities for IoT devices.
- Scalability and flexibility offered by AWS infrastructure.
Why Secure Access Matters
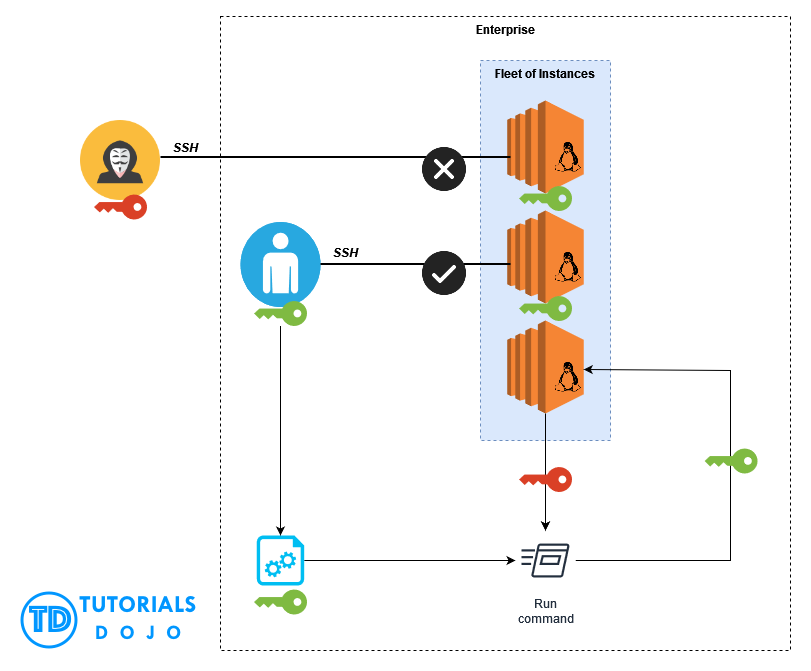
In the era of digital transformation, securing access to IoT devices is paramount. Cyber threats are becoming increasingly sophisticated, and unprotected IoT devices can serve as entry points for malicious actors. By leveraging SSH on AWS, organizations can significantly reduce the risk of unauthorized access and data breaches.
Understanding IoT Security Challenges
IoT devices often lack the robust security features found in traditional IT systems. This makes them vulnerable to attacks such as brute force, man-in-the-middle, and Distributed Denial of Service (DDoS). Implementing secure access protocols like SSH on AWS addresses these vulnerabilities by providing end-to-end encryption and authentication mechanisms.
According to a report by Gartner, the number of IoT devices is expected to surpass 25 billion by 2025. With this rapid growth, the importance of secure access cannot be overstated. Organizations must prioritize security to protect sensitive data and maintain operational integrity.
Setting Up SSH on AWS
Setting up SSH on AWS involves several steps, including configuring security groups, generating SSH keys, and connecting to instances. This section provides a detailed walkthrough of the process, ensuring that you can establish secure connections to your IoT devices hosted on AWS.
Step-by-Step Guide
- Launch an EC2 Instance: Start by launching an Amazon EC2 instance to serve as the gateway for your IoT devices.
- Configure Security Groups: Adjust security group settings to allow SSH access from your IP address.
- Generate SSH Keys: Use the AWS Management Console or command-line tools to generate SSH key pairs.
- Connect to the Instance: Use the SSH client on your local machine to connect to the EC2 instance securely.
By following these steps, you can ensure that your IoT devices are accessible only through secure channels, minimizing the risk of unauthorized access.
Configuring IoT Devices for SSH
Once the AWS infrastructure is set up, the next step is to configure your IoT devices to support SSH connections. This involves installing SSH servers on the devices and ensuring they are properly configured for secure communication.
Best Practices for IoT Device Configuration
- Install SSH Server: Use lightweight SSH servers like Dropbear or OpenSSH for resource-constrained IoT devices.
- Enable Firewall Rules: Configure firewall settings to restrict access to trusted IP addresses.
- Update Firmware Regularly: Keep device firmware up to date to patch known vulnerabilities.
These practices not only enhance security but also improve the overall performance and reliability of your IoT infrastructure.
Best Practices for Secure IoT SSH AWS
Implementing secure access for IoT devices on AWS requires adherence to best practices. This section outlines key strategies to ensure the highest level of security for your IoT SSH AWS setup.
Key Strategies
- Use Strong Passwords: Enforce strong password policies to prevent brute force attacks.
- Implement Multi-Factor Authentication (MFA): Add an extra layer of security by requiring MFA for SSH access.
- Monitor Access Logs: Regularly review SSH access logs to detect suspicious activities.
By following these best practices, you can significantly reduce the risk of security breaches and ensure the integrity of your IoT infrastructure.
Common SSH AWS Issues and Solutions
While SSH on AWS offers robust security features, users may encounter issues during setup and operation. This section addresses common challenges and provides practical solutions to overcome them.
Troubleshooting Guide
Issue: Unable to Connect to EC2 Instance
Solution: Verify that the security group settings allow SSH access from your IP address. Ensure that the SSH key pair matches the one used during instance creation.
Issue: Slow SSH Connection
Solution: Optimize network settings and ensure that the EC2 instance is located in a region close to your physical location.
Enhancing Security with SSH Keys
SSH keys provide a secure alternative to password-based authentication, reducing the risk of unauthorized access. This section explores the benefits of using SSH keys and provides guidance on their implementation.
Advantages of SSH Keys
- Eliminates the need for password-based authentication.
- Provides stronger security through cryptographic algorithms.
- Facilitates seamless access for authorized users.
By adopting SSH keys as part of your security strategy, you can enhance the protection of your IoT devices on AWS.
Integrating IoT with AWS Services
AWS offers a wide range of services that can be integrated with IoT devices to enhance functionality and security. This section examines how these services can be leveraged to create a comprehensive IoT SSH AWS solution.
Key AWS Services
- AWS IoT Core: Provides secure and reliable communication between IoT devices and AWS.
- AWS Lambda: Enables serverless computing for processing IoT data.
- Amazon S3: Offers scalable storage for IoT data backups and logs.
By integrating these services, you can build a robust IoT infrastructure that supports secure SSH access and advanced data processing capabilities.
Monitoring and Managing IoT SSH Connections
Effective monitoring and management of IoT SSH connections are essential for maintaining security and operational efficiency. This section discusses tools and techniques for monitoring SSH activity and managing IoT devices on AWS.
Monitoring Tools
- AWS CloudTrail: Tracks API calls and SSH access attempts for auditing purposes.
- AWS CloudWatch: Provides real-time monitoring of SSH connections and system performance.
These tools enable you to detect and respond to potential security threats quickly, ensuring the continued integrity of your IoT infrastructure.
Future of IoT SSH AWS
As technology continues to advance, the future of IoT SSH AWS looks promising. Innovations in cybersecurity, cloud computing, and IoT devices will further enhance the capabilities of this solution, offering unprecedented levels of security and functionality.
Emerging trends such as quantum computing and artificial intelligence are expected to play a significant role in shaping the future of IoT SSH AWS. Organizations that embrace these advancements will be better positioned to meet the evolving demands of the digital age.
Conclusion
In conclusion, Access IoT SSH AWS represents a powerful solution for securing IoT devices in the cloud. By following the guidelines and best practices outlined in this article, you can implement a robust security framework that protects your IoT infrastructure from cyber threats. Remember to regularly update your systems, monitor access logs, and stay informed about the latest advancements in cybersecurity.
We invite you to share your thoughts and experiences in the comments section below. Your feedback is invaluable in helping us improve and expand our content. Additionally, feel free to explore other articles on our site for more insights into the world of IoT and cybersecurity.