Remote SSH IoT has become a cornerstone of modern technology, enabling seamless communication and control of devices over the internet. As the Internet of Things (IoT) continues to expand, understanding how to securely connect and manage devices remotely is essential for both professionals and enthusiasts. This guide will delve into the intricacies of remote SSH IoT, providing practical examples and actionable insights to help you master this powerful technology.
Whether you're a developer, hobbyist, or IT professional, remote SSH IoT offers a world of possibilities. From automating home appliances to monitoring industrial equipment, SSH provides a secure and reliable method for accessing IoT devices remotely. This article aims to equip you with the knowledge and tools necessary to harness the full potential of remote SSH IoT.
By the end of this guide, you'll have a comprehensive understanding of how remote SSH IoT works, its benefits, challenges, and best practices. Let's dive in and explore the fascinating world of remote SSH IoT!
Table of Contents
- Introduction to Remote SSH IoT
- How SSH Works in IoT
- Benefits of Remote SSH IoT
- Challenges in Implementing Remote SSH IoT
- Securing Your Remote SSH IoT Setup
- Tools and Software for Remote SSH IoT
- Practical Example of Remote SSH IoT
- Best Practices for Remote SSH IoT
- Future Trends in Remote SSH IoT
- Conclusion and Next Steps
Introduction to Remote SSH IoT
Remote SSH IoT is a technology that allows users to securely access and manage IoT devices over the internet using the SSH protocol. SSH, or Secure Shell, is a cryptographic network protocol designed to provide secure communication between devices. In the context of IoT, SSH plays a critical role in ensuring that data transmitted between devices remains confidential and tamper-proof.
IoT devices are increasingly being deployed in various sectors, including healthcare, manufacturing, and smart homes. Remote SSH IoT enables these devices to be monitored and controlled remotely, enhancing efficiency and reducing the need for physical intervention. This section will explore the basics of SSH and its application in IoT environments.
What is SSH?
SSH is a network protocol that facilitates secure data communication, remote command execution, and other network services. It provides a secure channel over an unsecured network by encrypting all data transmitted between devices. SSH is widely used in IT infrastructure for remote administration and file transfers.
Why Use SSH for IoT?
SSH offers several advantages for IoT applications, including:
- Security: SSH encrypts data, ensuring that sensitive information remains protected from unauthorized access.
- Reliability: SSH connections are stable and resistant to network disruptions.
- Flexibility: SSH supports a wide range of commands and operations, making it versatile for various IoT use cases.
How SSH Works in IoT
Understanding how SSH operates is crucial for effectively implementing remote SSH IoT. The protocol establishes a secure connection between a client and a server, ensuring that all communication is encrypted and authenticated. This section will break down the key components of SSH and explain how they apply to IoT devices.
Key Components of SSH
SSH relies on several key components to ensure secure communication:
- Public and Private Keys: These cryptographic keys are used for authentication, ensuring that only authorized users can access the IoT device.
- Encryption Algorithms: SSH uses advanced encryption algorithms to protect data during transmission.
- Port Forwarding: SSH allows users to forward specific ports, enabling secure access to services running on IoT devices.
SSH in IoT Architecture
In an IoT environment, SSH can be implemented to secure communication between devices, gateways, and cloud platforms. By configuring SSH on IoT devices, users can remotely access device settings, update firmware, and monitor performance metrics without compromising security.
Benefits of Remote SSH IoT
Remote SSH IoT offers numerous advantages that make it an attractive solution for managing IoT devices. This section will highlight the key benefits of using SSH in IoT applications.
Enhanced Security
SSH provides robust security features, such as encryption and authentication, which protect IoT devices from cyber threats. By using SSH, users can ensure that their devices remain secure even when accessed over public networks.
Remote Access and Management
One of the primary benefits of remote SSH IoT is the ability to manage devices from anywhere in the world. Whether you're troubleshooting a device or performing routine maintenance, SSH allows you to do so without being physically present.
Scalability
SSH is highly scalable, making it suitable for large-scale IoT deployments. It can handle multiple devices and users simultaneously, ensuring that your IoT infrastructure remains efficient and responsive.
Challenges in Implementing Remote SSH IoT
While remote SSH IoT offers many benefits, there are also challenges that need to be addressed. This section will explore some of the common obstacles faced when implementing SSH in IoT environments.
Security Vulnerabilities
Despite its robust security features, SSH is not immune to vulnerabilities. Weak passwords, outdated software, and misconfigured settings can expose IoT devices to potential attacks. It's essential to follow best practices to mitigate these risks.
Complexity
Configuring SSH on IoT devices can be complex, especially for users without a technical background. Understanding the intricacies of SSH keys, port forwarding, and firewalls requires a certain level of expertise.
Network Constraints
IoT devices often operate in environments with limited bandwidth or unstable connectivity. This can impact the performance of SSH connections, leading to delays or disconnections. Optimizing network settings is crucial for ensuring reliable SSH communication.
Securing Your Remote SSH IoT Setup
Securing your remote SSH IoT setup is paramount to protecting your devices and data. This section will provide practical tips and strategies for enhancing the security of your SSH configuration.
Use Strong Authentication
Implementing strong authentication mechanisms, such as public and private keys, is essential for securing SSH connections. Avoid using weak passwords and enable two-factor authentication whenever possible.
Regularly Update Software
Keeping your SSH software up to date is crucial for addressing vulnerabilities and ensuring compatibility with the latest security protocols. Regularly update your IoT devices and servers to protect against potential threats.
Monitor Access Logs
Monitoring SSH access logs can help detect unauthorized access attempts and suspicious activity. By analyzing these logs, you can identify potential security breaches and take corrective action promptly.
Tools and Software for Remote SSH IoT
Several tools and software solutions are available to facilitate remote SSH IoT implementation. This section will introduce some of the most popular options and explain how they can be used to enhance your IoT setup.
OpenSSH
OpenSSH is an open-source software suite that provides secure communication over unsecured networks. It is widely used for remote SSH IoT applications and offers a range of features, including encryption, authentication, and port forwarding.
Putty
Putty is a popular SSH client for Windows users. It provides a user-friendly interface for establishing SSH connections and supports various authentication methods, making it an ideal choice for remote SSH IoT.
SSH Tunnels
SSH tunnels allow users to securely access services running on IoT devices by forwarding specific ports. This feature is particularly useful for applications that require secure communication, such as file transfers and database access.
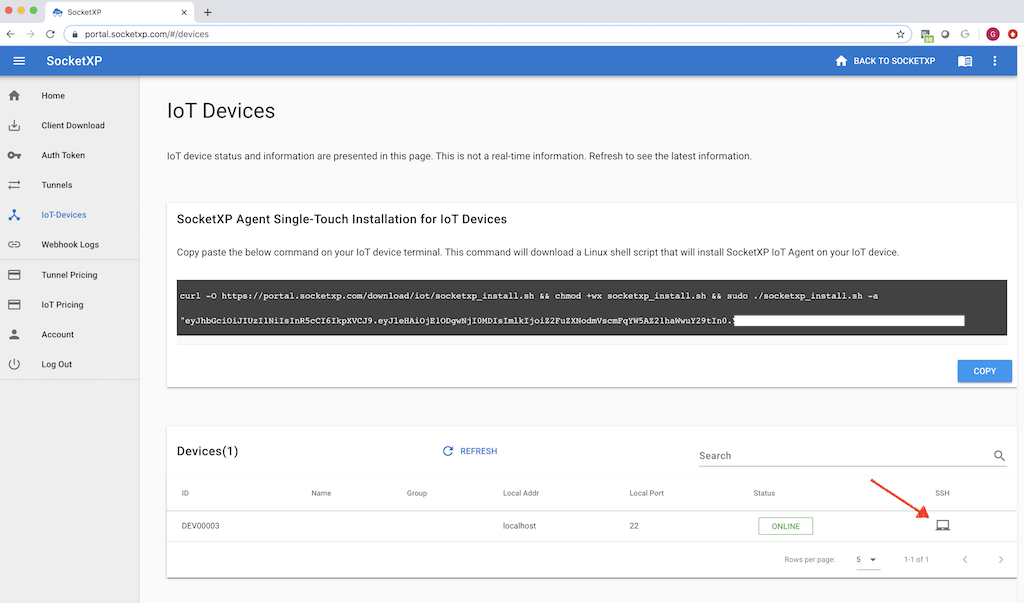
Practical Example of Remote SSH IoT
To better understand how remote SSH IoT works in practice, let's consider a real-world example. Imagine you're managing a smart home system that includes IoT devices such as smart lights, thermostats, and security cameras. By configuring SSH on these devices, you can remotely access and control them from anywhere in the world.
Step-by-Step Guide
Here's a step-by-step guide to setting up remote SSH IoT for your smart home system:
- Install SSH software on your IoT devices.
- Generate public and private keys for authentication.
- Configure port forwarding on your router to allow remote access.
- Test the connection using an SSH client such as Putty or OpenSSH.
Best Practices for Remote SSH IoT
Adhering to best practices is essential for ensuring the success of your remote SSH IoT implementation. This section will provide actionable tips for optimizing your SSH configuration.
Limit Access to Authorized Users
Restrict SSH access to authorized users only by using strong authentication mechanisms and disabling password-based logins. This minimizes the risk of unauthorized access and enhances security.
Monitor Network Traffic
Regularly monitor network traffic to detect any unusual activity or potential security threats. By keeping a close eye on your network, you can quickly identify and address issues before they escalate.
Document Your Configuration
Maintaining detailed documentation of your SSH configuration is crucial for troubleshooting and future reference. Include information such as IP addresses, port numbers, and key pairs to ensure that your setup remains organized and manageable.
Future Trends in Remote SSH IoT
The future of remote SSH IoT looks promising, with advancements in technology driving innovation in this field. This section will explore some of the emerging trends and technologies that are shaping the future of remote SSH IoT.
Quantum-Resistant Cryptography
As quantum computing becomes more prevalent, there is a growing need for quantum-resistant cryptography to secure SSH connections. This technology ensures that SSH remains secure even against advanced cyber threats.
Edge Computing
Edge computing is revolutionizing IoT by enabling data processing at the edge of the network. By integrating SSH with edge computing, users can enhance the security and efficiency of their IoT setups.
Artificial Intelligence
AI-powered solutions are increasingly being used to optimize SSH configurations and detect potential security threats. These technologies offer new possibilities for enhancing the performance and security of remote SSH IoT.
Conclusion and Next Steps
Remote SSH IoT is a powerful technology that offers numerous benefits for managing IoT devices securely and efficiently. By understanding the principles of SSH and following best practices, you can harness its full potential and stay ahead in the rapidly evolving world of IoT.
We encourage you to take the next step by implementing SSH in your IoT projects and exploring the various tools and resources available. Don't forget to share your thoughts and experiences in the comments section below, and consider exploring other articles on our site for more insights into the world of IoT.