In today's interconnected world, securing IoT devices has become a top priority for both individuals and businesses. The RemoteIoT firewall tutorial aims to guide you through the essential steps of protecting your network from potential cyber threats. By understanding how this firewall works, you can significantly enhance the security of your IoT infrastructure.
As more devices connect to the internet, the risk of unauthorized access and data breaches increases. RemoteIoT firewall offers a robust solution to safeguard your network by filtering traffic and blocking malicious actors. This tutorial will provide you with a detailed understanding of its features, configuration, and best practices for implementation.
Whether you're a beginner or an experienced IT professional, this RemoteIoT firewall tutorial will equip you with the knowledge needed to secure your IoT ecosystem effectively. Let's dive in and explore how to protect your devices and data.
Table of Contents
- Introduction to RemoteIoT Firewall
- Why RemoteIoT Firewall is Essential
- Key Features of RemoteIoT Firewall
- Installation Process
- Configuration Steps
- Advanced Settings and Customization
- Best Practices for Security
- Troubleshooting Common Issues
- RemoteIoT Firewall vs. Other Solutions
- Future Trends in IoT Security
Introduction to RemoteIoT Firewall
The RemoteIoT firewall is a cutting-edge solution designed to protect IoT networks from cyber threats. It acts as a barrier between your devices and the internet, filtering incoming and outgoing traffic to ensure only legitimate connections are allowed.
What is IoT Security?
IoT security involves safeguarding internet-connected devices and networks from unauthorized access and cyberattacks. With billions of IoT devices in use worldwide, securing these systems is critical to protecting sensitive data and maintaining privacy.
How Does RemoteIoT Firewall Work?
RemoteIoT firewall operates by analyzing network traffic and applying predefined rules to determine whether to allow or block connections. It uses advanced algorithms to detect and prevent malicious activities, ensuring your IoT infrastructure remains secure.
Why RemoteIoT Firewall is Essential
Implementing a RemoteIoT firewall is crucial for maintaining the integrity and security of your IoT network. Without proper protection, your devices could be vulnerable to attacks such as DDoS, malware, and unauthorized access.
- Prevents unauthorized access to your network
- Protects sensitive data from being intercepted or stolen
- Reduces the risk of cyberattacks on IoT devices
Key Features of RemoteIoT Firewall
RemoteIoT firewall comes equipped with several powerful features that make it an ideal choice for securing IoT networks.
Real-Time Monitoring
With real-time monitoring, you can keep track of network activity and receive alerts for any suspicious behavior. This allows you to take immediate action to mitigate potential threats.
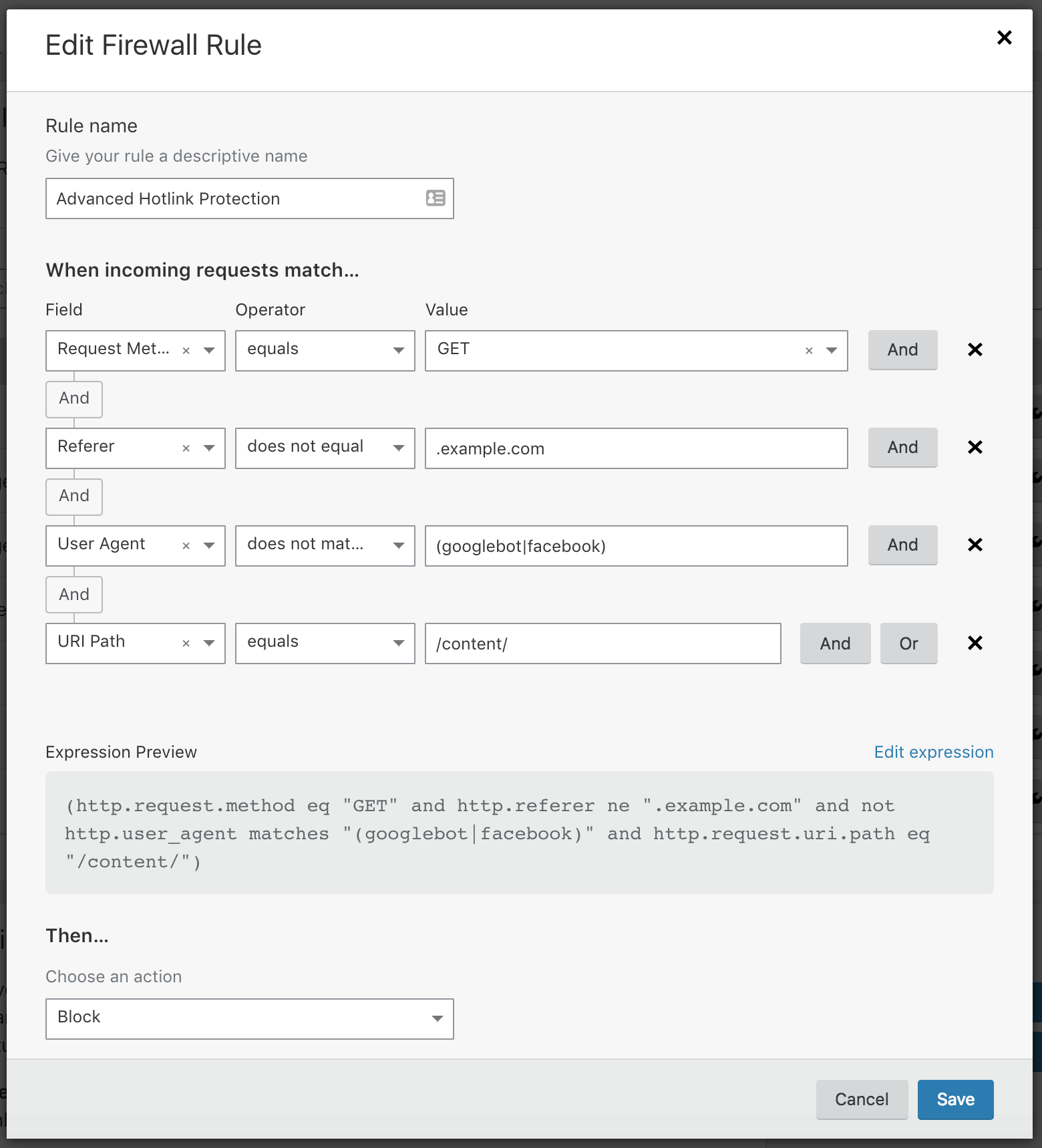
Customizable Rules
Create custom rules to suit your specific security needs. Whether you want to block certain IP addresses or allow only specific types of traffic, RemoteIoT firewall gives you the flexibility to tailor its functionality.
Advanced Threat Detection
Utilizing machine learning and artificial intelligence, RemoteIoT firewall can detect and respond to advanced threats in real-time, ensuring your network remains protected against evolving cyberattacks.
Installation Process
Installing RemoteIoT firewall is a straightforward process that can be completed in a few simple steps.
System Requirements
- Compatible operating system (Linux, Windows, macOS)
- Minimum 2 GB RAM
- At least 500 MB of free disk space
Step-by-Step Guide
Follow these steps to install RemoteIoT firewall on your system:
- Download the installation package from the official website
- Run the installer and follow the on-screen instructions
- Configure the firewall settings according to your requirements
- Test the installation to ensure it's functioning correctly
Configuration Steps
Once installed, configuring RemoteIoT firewall is essential to ensure it meets your security needs.
Basic Configuration
Start by setting up basic parameters such as network interfaces, IP addresses, and default rules. This ensures the firewall can properly monitor and filter traffic.
Advanced Configuration
For enhanced security, configure advanced settings such as port forwarding, NAT, and VLAN support. These options provide greater control over your network and help optimize performance.
Advanced Settings and Customization
RemoteIoT firewall offers a range of advanced settings that allow you to fine-tune its operation.
Custom Rule Sets
Create custom rule sets to address specific security concerns. For example, you can block traffic from certain countries or allow only encrypted connections.
Integration with Other Tools
Integrate RemoteIoT firewall with other security tools such as intrusion detection systems (IDS) and antivirus software for comprehensive protection.
Best Practices for Security
Adopting best practices is vital for maximizing the effectiveness of RemoteIoT firewall.
- Regularly update the firewall software to ensure you have the latest features and security patches
- Monitor network activity and adjust rules as needed to address new threats
- Implement strong authentication mechanisms to prevent unauthorized access
Troubleshooting Common Issues
Even with proper configuration, issues may arise. Here are some common problems and their solutions:
- Connection Issues: Verify firewall rules and ensure the correct network settings are applied
- Performance Problems: Optimize rules and disable unnecessary features to improve performance
- Alert Overload: Fine-tune alert thresholds to reduce the number of false positives
RemoteIoT Firewall vs. Other Solutions
When comparing RemoteIoT firewall to other IoT security solutions, several factors set it apart:
- Advanced threat detection capabilities
- Customizable rules and settings
- Integration with third-party security tools
Future Trends in IoT Security
As IoT technology continues to evolve, so too will the methods used to secure these networks. Some future trends in IoT security include:
- Increased use of artificial intelligence and machine learning for threat detection
- Development of more robust encryption protocols
- Greater emphasis on privacy and data protection regulations
Conclusion
Securing your IoT network with a RemoteIoT firewall is essential in today's digital landscape. By following the steps outlined in this tutorial, you can effectively protect your devices and data from cyber threats. Remember to regularly update your firewall and adopt best practices to ensure maximum security.
We invite you to share your thoughts and experiences with RemoteIoT firewall in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT security and related topics.
Data source: RemoteIoT Official Website
![[PDF] Firewall free tutorial for Beginners](https://www.computer-pdf.com/documents/covers/0175-firewall-tutorial.pdf.png)