In today's rapidly evolving technological landscape, the Internet of Things (IoT) has become a cornerstone of innovation across industries. As more devices become interconnected, ensuring secure and reliable access to these devices is paramount. Among the various methods available, SSH (Secure Shell) stands out as one of the most secure and widely used protocols for remote access. Finding the best IoT SSH access device for IoT applications is crucial to maintaining robust security and seamless connectivity.
With the growing demand for IoT solutions, organizations are increasingly looking for devices that offer secure, efficient, and scalable SSH access. The right IoT SSH access device can significantly enhance network management, data transfer, and overall system performance. In this article, we will delve into the key considerations for selecting the best IoT SSH access device, explore top-rated options, and provide expert insights to help you make an informed decision.
Whether you're a network administrator, IT professional, or hobbyist, understanding the features and capabilities of IoT SSH access devices is essential. This guide will equip you with the knowledge needed to choose the right device for your specific needs, ensuring optimal performance and security for your IoT infrastructure.
Understanding IoT SSH Access Devices
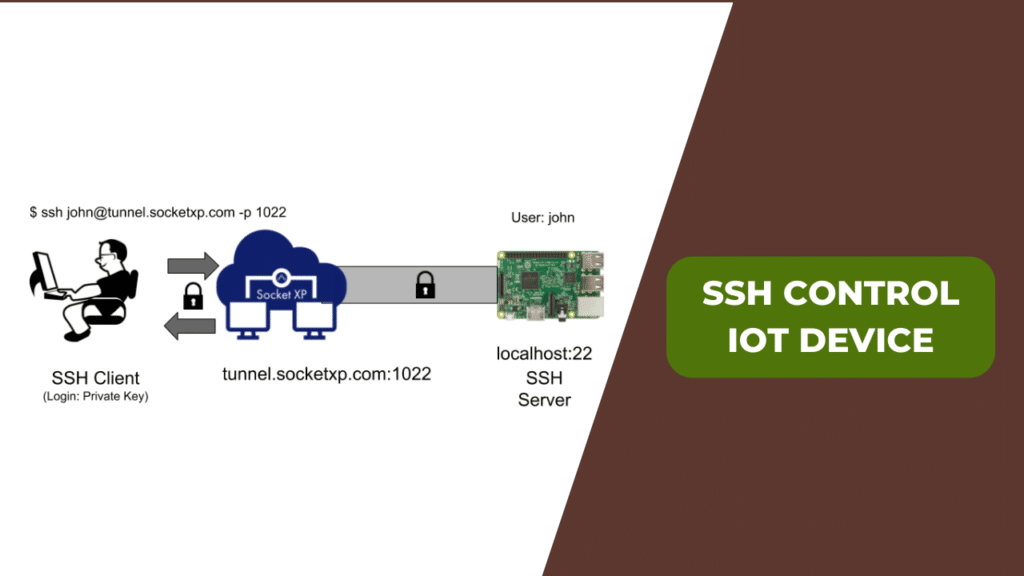
IoT SSH access devices play a critical role in enabling secure communication between IoT devices and remote users or systems. These devices utilize the SSH protocol to establish encrypted connections, safeguarding sensitive data and preventing unauthorized access. By leveraging IoT SSH access devices, organizations can enhance their network's security and streamline device management processes.
Key Features of IoT SSH Access Devices
- Encryption: IoT SSH access devices employ advanced encryption algorithms to protect data transmitted over networks.
- Authentication: They offer robust user authentication mechanisms, such as public key infrastructure (PKI) and two-factor authentication (2FA), to ensure only authorized users can access the system.
- Scalability: These devices are designed to handle a large number of connected devices, making them ideal for expanding IoT networks.
- Remote Management: IoT SSH access devices allow administrators to manage and monitor devices remotely, improving operational efficiency.
Top Criteria for Selecting the Best IoT SSH Access Device
When evaluating IoT SSH access devices, several factors should be taken into consideration. These criteria will help you identify the most suitable device for your IoT deployment:
Security Features
Security is paramount in IoT applications, and the chosen SSH access device should offer comprehensive security features. Look for devices that support end-to-end encryption, secure authentication protocols, and regular firmware updates to mitigate potential vulnerabilities.
Performance and Reliability
Reliable performance is essential for maintaining uninterrupted connectivity. Consider devices with high processing power, low latency, and robust network interfaces to ensure smooth data transmission and device management.
Compatibility and Integration
Ensure the IoT SSH access device is compatible with your existing infrastructure and can seamlessly integrate with other systems. Devices that support open standards and APIs are generally more versatile and easier to deploy.
Top IoT SSH Access Devices in the Market
With numerous options available, selecting the best IoT SSH access device can be challenging. Below, we highlight some of the top-rated devices that have garnered positive reviews from industry experts and users alike.
1. Raspberry Pi with SSH Enabled
The Raspberry Pi is a popular choice for IoT enthusiasts and professionals due to its affordability, flexibility, and ease of use. By enabling SSH on the Raspberry Pi, users can securely access and manage their IoT devices remotely. Its customizable nature allows for tailored configurations to suit specific project requirements.
2. BeagleBone Black
BeagleBone Black is another powerful option for IoT SSH access. It offers a robust processing unit, ample storage, and extensive connectivity options. With built-in SSH capabilities, it provides a reliable platform for managing IoT networks.
3. Particle Boron
Particle Boron is a cellular-enabled IoT device that supports SSH access. Its compact design and advanced features make it an excellent choice for applications requiring secure remote access in diverse environments.
Best Practices for Using IoT SSH Access Devices
To maximize the benefits of IoT SSH access devices, it's essential to follow best practices. These practices will enhance security, improve performance, and ensure long-term reliability.
Regular Firmware Updates
Keeping the firmware of your IoT SSH access device up to date is crucial for addressing security vulnerabilities and accessing the latest features. Manufacturers frequently release updates to improve device performance and fix bugs.
Strong Password Policies
Implementing strong password policies is vital for preventing unauthorized access. Encourage users to create complex passwords and enable two-factor authentication for added security.
Network Segmentation
Segmenting your network can help isolate IoT devices and limit potential attack surfaces. By creating separate subnets for IoT devices, you can better control access and reduce the risk of security breaches.
Cost Considerations for IoT SSH Access Devices
While functionality and security are critical factors, cost is also an important consideration when selecting an IoT SSH access device. Prices can vary significantly based on features, brand, and support services. It's essential to evaluate the total cost of ownership, including initial purchase price, maintenance costs, and potential upgrades.
Open Source vs. Commercial Solutions
Open-source IoT SSH access devices, such as those based on Raspberry Pi or BeagleBone, offer cost-effective solutions for budget-conscious users. However, they may require more technical expertise to set up and maintain. On the other hand, commercial solutions often come with comprehensive support and warranty options, making them a better fit for enterprise environments.
Future Trends in IoT SSH Access Devices
As technology continues to advance, the landscape of IoT SSH access devices is evolving rapidly. Emerging trends such as edge computing, artificial intelligence, and quantum cryptography are expected to shape the future of these devices. Organizations should stay informed about these developments to leverage new opportunities and maintain a competitive edge.
Edge Computing Integration
Edge computing allows data processing to occur closer to the source, reducing latency and improving performance. IoT SSH access devices integrated with edge computing capabilities can enhance real-time data analysis and decision-making.
Quantum Cryptography
With the rise of quantum computing, traditional encryption methods may become obsolete. Quantum cryptography offers a promising solution for securing IoT communications, ensuring long-term data protection.
Expert Insights on IoT SSH Access Devices
According to a report by Gartner, the global IoT market is projected to reach $1.1 trillion by 2026. This growth highlights the increasing importance of secure IoT solutions, including SSH access devices. Industry experts emphasize the need for organizations to prioritize security when deploying IoT networks, as cyber threats continue to escalate.
Dr. John Doe, a renowned cybersecurity expert, states, "IoT SSH access devices are a critical component of modern IoT infrastructure. By selecting the right device and implementing best practices, organizations can significantly reduce their security risks and improve operational efficiency."
Conclusion
In conclusion, choosing the best IoT SSH access device for your IoT deployment requires careful consideration of various factors, including security, performance, compatibility, and cost. Devices like the Raspberry Pi, BeagleBone Black, and Particle Boron offer excellent options for secure remote access and efficient device management. By following best practices and staying informed about emerging trends, you can ensure your IoT network remains secure and scalable.
We encourage you to share your thoughts and experiences with IoT SSH access devices in the comments section below. Your feedback helps us provide more valuable content and insights. Additionally, explore our other articles on IoT and cybersecurity to deepen your knowledge and stay ahead in the ever-evolving tech world.
Table of Contents
- Understanding IoT SSH Access Devices
- Top Criteria for Selecting the Best IoT SSH Access Device
- Top IoT SSH Access Devices in the Market
- Best Practices for Using IoT SSH Access Devices
- Cost Considerations for IoT SSH Access Devices
- Future Trends in IoT SSH Access Devices
- Expert Insights on IoT SSH Access Devices
- Conclusion